CyberSmart Technologies has rebranded.
Welcome to Rollcage Defence.
DMARC – One protocol to bind them all
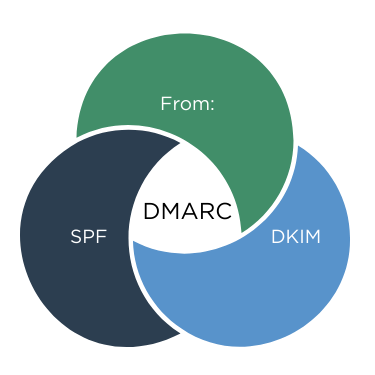
DMARC tells the receiving email server what do when SPF and DKIM policy checks fail. However DMARC performs another vital step. DMARC checks that that the domain of the author, as seen by the end-user fully the domain validated by…